Contents
As the internet continues to grow and expand, so too does the prevalence of online scams that target unsuspecting consumers. From phishing scams to online shopping scams and everything in between, cybercriminals are finding new and creative ways to steal personal information and scam people out of their hard-earned money.
Fraudsters are always improving on their deceptive and lucrative scamming methods alongside the continuous development of the Internet.
Let’s look closely at some of the most sophisticated scams surfacing on the Internet.

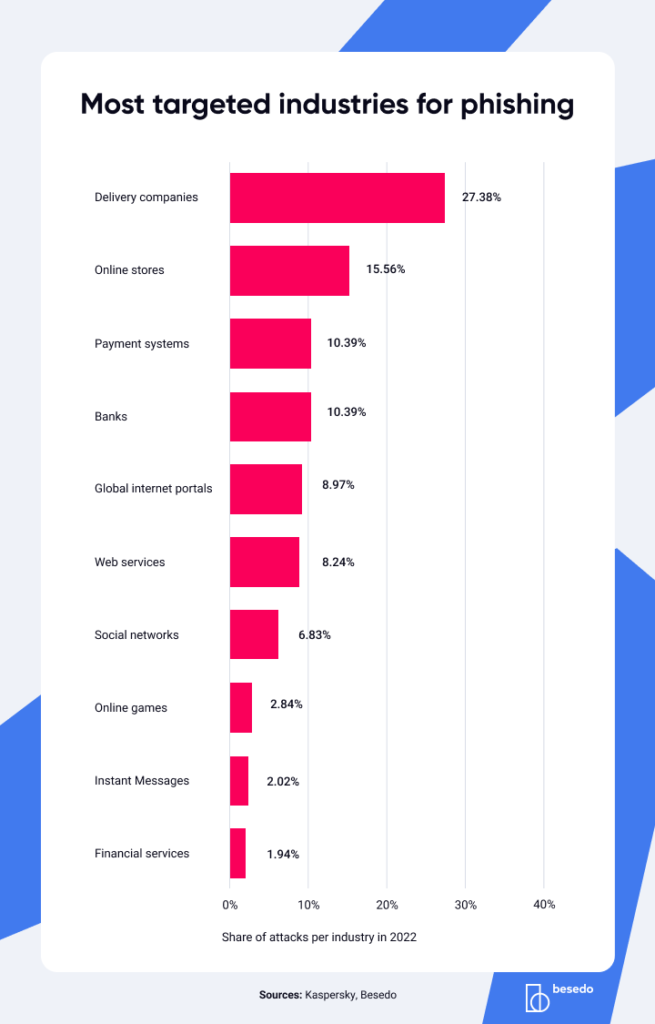
Phishing scams
Phishing scams are a persistent and pervasive threat in the online world, and they’re only becoming more sophisticated over time. Cybercriminals use a variety of tactics to trick people into divulging sensitive information, such as creating fake login pages or crafting convincing emails that appear to come from trusted sources. By manipulating the emotions of their victims and exploiting their trust in established institutions, phishers can steal their login credentials, financial information, and identities.
One particularly insidious form of phishing is “spear-phishing,” which involves tailoring the scam to a specific individual or group. For example, a cybercriminal might research an organization’s hierarchy and send a convincing email to a senior executive, asking them to provide sensitive information or transfer funds to a fraudulent account. This attack is more difficult to detect and is often successful in obtaining sensitive information.
The Anti-Phishing Working Group (APWG) reports that the number of phishing attacks is rising, with 1,270,883 reported in the third quarter of 2022 alone. This is a concerning trend that underscores the need for increased awareness and education about online security. To protect yourself against phishing attacks, being vigilant and cautious when receiving unsolicited emails or messages is important. Verify the sender’s identity and scrutinize any requests for sensitive information. Additionally, use two-factor authentication whenever possible.
And while this may sound like a “have you tried turning it off and then on again”-advice: Keep your antivirus and security software up-to-date to help detect and prevent these attacks. By staying informed and taking proactive steps to protect yourself, you can minimize the risk of falling victim to a phishing scam.
Example
A cybercriminal sends an email to a user claiming to be from their bank, stating that their account has been compromised and requesting that they click on a link to reset their password. The link takes them to a fake website that looks identical to their bank’s website, where they enter their login credentials and personal information, which the cybercriminals then use to access their account.
How to avoid
Always be suspicious of emails or messages asking for personal information. Check the sender’s email address or message source to ensure it’s legitimate.
And for the love of everything, avoid clicking on links in emails or messages. If you must see this link, type the URL directly into your browser or use a bookmark to access the website.
Online shopping and website scams
Have you ever stumbled upon a website selling the latest gadgets at dirt-cheap prices? Sounds too good to be true, right? That’s because it probably is. Online shopping scams are everywhere, with fraudsters setting up fake e-commerce websites to swindle people out of their hard-earned cash.
These scammers use all sorts of tricks to fool you into thinking their website is legit, like using fake product images and reviews and offering insane discounts that you won’t find anywhere else. Once you place your order and make a payment, they disappear into thin air, leaving you with nothing but a lighter wallet.
According to the FBI’s Internet Crime Complaint Center (IC3), there were over 28,500 reported cases of online shopping scams in 2020, just the reported ones. So it’s important to be cautious and protect yourself when shopping online ?
To avoid getting ripped off, always check for trusted third-party seals like Norton Secured or McAfee Secure, and read customer reviews to make sure the website is legit. And if a deal seems too good to be true, it probably is.
Better to be safe than sorry, right?
If you end up falling victim to an online shopping scam, don’t panic.
Contact your bank or credit card company immediately to report the fraud and dispute any charges. You can also report the scam to the website and law enforcement agencies to help prevent others from getting scammed.
Example
A user comes across a website selling the latest iPhone at a price that’s too good to be true. They place an order and pay, only to receive a fake tracking number or no response. The scammer has taken their money and disappeared.
How to Avoid
Always verify the legitimacy of an online retailer before making a purchase. Check the website’s reviews and ratings, and look for trusted third-party seals such as Norton Secured or McAfee Secure. Be cautious of deals that seem too good to be true.
Impersonation scams
Phishing scams are very well-known. However, a variation, the impersonation scam, has boomed over the past few years, impacting both users’ online safety and companies’ reputation.
These phishing emails might seem completely genuine as they look nearly identical to those of reputable and reliable websites, including Google or Apple, and often bypass spam filters. Like many fraud schemes, impersonation scams are based on trust.
The popular streaming service Netflix was the target of an email phishing scam in Ireland that was sent to thousands of subscribers on the pretext of a maintenance and verification issue. Like the fake website scams previously mentioned, these malicious emails, looking like perfect replicas of Netflix emails, featured a link to update credit card information or login credentials. However, the link did not direct users to the Netflix website but to a site managed by scammers.
Scams often target popular brands with a large user base to lure subscribers into giving out personal information. Not only is this dangerous for the customer, but it also threatens the brand’s reputation.
Romance mule scams
Online dating sites have been one of romance scammers’ preferred hunting grounds to find their next victim.
The FBI’s online crime division recently flagged an alarmingly growing trend in the romance scam department. Online dating scammers have expanded their romance scam strategies by adding a new dark twist and taking advantage of their victims in a whole new way. This dating scam turns love-seekers into unwittingly recruited criminals known as money mules.
The fraudster will spend time getting to know the victim and building a rapport, often sending gifts or money to gain their trust. Once the victim is emotionally invested, the fraudster will ask them to receive and transfer money or goods on their behalf, claiming that they cannot do so themselves due to personal or financial difficulty.
Here’s how they work. The scammers, pretending to be American or European citizens living or working abroad, groom their victims for several months by establishing a supposedly trustworthy relationship with them. They then have their victim act as a financial middle-person in various fraudulent activities. There are many ways victims can unwittingly help fraudsters. For instance, they can print and post packages or letters often containing counterfeit checks, or in other cases, pick up money at Western Union and forward it to another place. They could even open a bank account under the pretense of sending and receiving payment directly, except that these accounts are unknowingly used to aid criminal activities.
Romance mule victims often do not know they are a part of these fraud schemes or criminal activities until it’s too late. Despite the victims not losing money, the FBI warns that they might face legal or financial consequences for participating in such a scheme.
The Telegraph reported a story about a 61-year-old British man tricked by fraudsters to fund terrorists in this exact way. He believed he was corresponding with a wealthy businesswoman he met on an online dating site. The woman claimed she needed her money in the UK to pay her European employees. The man would then send checks on her behalf, becoming inadvertently and unknowingly part of a fraud scheme.
7 jaw-dropping stats about cybercrime you can’t afford to ignore
- Phishing is the reigning king of cybercrime, with a staggering 3.4 billion spam emails sent out every day!
- Heads up: stolen credentials are the leading cause of data breaches. Make sure to beef up your password security to protect your online presence.
- Google deserves a round of applause for blocking a whopping 100 million phishing emails daily. Talk about being on the front lines of cyber defense.
- Over 48% of emails sent in 2022 were spam – that’s a whole lot of unsolicited mail cluttering up your inbox.
- Russia has earned itself a less than honorable distinction in the cyber world – over 20% of phishing emails originate from the land of balalaikas and nesting dolls.
- 83% of UK businesses that were hit by a cyberattack in 2022 reported phishing as the attack type. It’s time to take this threat seriously.
- Brace yourself for the cost of cybercrime – the average data breach against an organization costs over $4 million.
Staying ahead of the scammers
With fraudsters persistently refining their scamming techniques, companies must always be one step ahead in preventing these scams from protecting their users and keeping them safe on their sites.
Marketplace leakage refers to losing your users from operating on your platform and continuing their conversations beyond your site’s security measures. This technique of luring users away from your site is used in the scam examples mentioned in this article and dramatically increases the risk of your users being scammed.
Marketplace leakage can be avoided by improving your content moderation efforts. By ensuring accurate automated moderation, you can instantly spot and prevent any content that draws users away from your platform.